EDUCATION
How to Beware of Ransomware
Expert Tips to Hackproof Your Business
By Douglas McColloch
Companies in the 21st century enjoy a wide range of competitive advantages that were unavailable to previous generations of businesses. The use of the internet to automate ordering and billing, to manage inventory or to process payrolls can increase productivity, reduce waste and maximize efficiencies across departments.

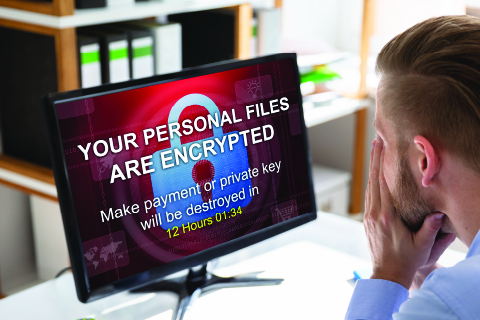
According to the FBI, the cost of ransomware attacks was $250 billion in 2020, with an average downtime of 19 days for the affected entities. As hackers’ tools grow more varied and sophisticated, expect that number to escalate in the coming years. Photo courtesy: Shutterstock
But all of that connectivity comes with its downsides, too—one of which is “ransomware,” which can be loosely defined as the practice of hacking into a company’s digital assets to “trap” the victim’s data by means of encryption. That can cause an irretrievable loss of assets—and even whole enterprise systems, depending on the size and scope of the hack—unless a ransom is paid, generally in an untraceable form of cryptocurrency such as Bitcoin.
The costs to businesses from ransomware are mounting. According to a recent study from the Federal Bureau of Investigation (FBI), ransomware costs were an estimated $250 billion in 2020, with an average downtime of 19 days for impacted companies.
In fact, the FBI study noted, a company’s downtime costs averaged 20 times more than the amount of ransom being extracted. An example of that occurred in 2019, when the municipal government of Baltimore, Maryland, was targeted by ransomware hackers. The amount of ransom the city paid—around $75,000—paled in comparison with the costs of the city’s downtime, which lasted more than a month at an expense of more than $18 million. And the threat is growing.
According to a paper published earlier this year by insurance giant Beazley Group, ransomware attacks increased 120% in 2019 over the previous year, with more than 60% of targets comprising small and medium-size businesses. According to the FBI, an attack occurs every 11 sec., so it’s clear that companies need to factor in the threats posed by ransomware when assessing the strength of their online data and security systems and make plans to fortify those potential targets against future attacks.
A recent SEMA Education webinar, “Ransomware—What SEMA Manufacturers, Retailers and WDs Can Do to Mitigate Threats,” aimed to demystify the subject, with a panel of industry experts providing guidance into best practices that can minimize if not eliminate the threat of a ransomware attack.
Identifying Modes of Attack
Nearly 90% of IT professionals and 75% of the owners of small- and medium-size businesses agree that cyber threats such as ransomware attacks represent a significant and growing risk, according to a 2021 Malware Report published by Cybersecurity Insiders. So while there’s near-unanimity on the nature of the threat, many business owners remain unaware of the source of the greatest—and most preventable—causes of cyber attacks.
- Email hacks: “You’ve all heard of ‘phishing’ or ‘spear phishing’ or ‘business email compromise,’ but it’s really all the same thing,” said Bruce Grant, president and CEO of Estes Group, a managed IT company that works with mid-market businesses on building and strengthening their Enterprise Resource Planning systems. While other, more sophisticated forms of hacking have become more widely used in recent years, common email-compromising attempts still constitute more than 80% of malware attack vectors. While an email hack represents the most prevalent form of attack, it’s also one of the most preventable. Ways for businesses to minimize the chance of an email hack include implementing greater use of email filters and added authentication layers; regular changes of employee passwords and blocking reuse of previous passwords; and educating employees to identify and report suspicious emails to their company IT departments.
- Fake domains: Another frequent means of entry used by hackers involves so-called “domain spoofing,” some form of which is used in up to 45% of all cyber attacks. It occurs when hackers use a counterfeit or “spoofed” web domain or email address to give the false impression of a legitimate company or individual. Generally, emails are the preferred mode of entry, but sometimes whole websites with slightly altered domain names are used. Even cybersecurity consulting companies aren’t immune from it. “Someone literally bought a similar domain to our company and tried to get access to some of our key employees through domain spoofing,” Grant said. Grant provided a little old-school advice here: “A few years ago, attacks were simple. There was a Nigerian prince trying to give you money, and you just didn’t click on that. But while the attacks have gotten much more sophisticated, the thinking is the same: ‘If you don’t trust it, don’t click on it.’”
Other Vulnerabilities
If email were the only attack vector hackers could exploit, the problem of ransomware could be greatly minimized with the simple fixes mentioned previously, but there are numerous ports of entry that hackers can exploit now, as Brad Feakes, Estes Group senior vice president, reminded the panel. The internet, for one, is a potential source of “infiltration dressed as information.”
- Apps and e-commerce: A related source of infiltration via malware is in applications—especially the apps needed to run an e-commerce site. “One subject that doesn’t get as much press as it probably should is the idea of applications,” Feakes said. “You should think of every application or program that you use for business purposes as a potential threat. Installing each application has its own limitations and risks in ways in which it can be hacked, whether it’s web-based or whether it’s installed onto a device within your network. The integrating of core systems to those devices can be especially challenging. Everybody likes e-commerce, right? E-commerce is a really big thing in the automotive industry. Customers want an easier experience, but those e-commerce sites create new entry points to your network.”
- IoT security challenges: Another factor that facilitates hacking is the interconnectivity of devices, which creates many portals of entry for would-be hostage takers. “We talk about the IoT or the ‘Internet of Things,’” Feakes explained. “This is the basic notion that we increasingly want to connect our devices. If you’re in an automotive industry, you have a bunch of different devices that might be serving a purpose functionally, and you want to connect to those that you can monitor and control them.” But he warned that those devices themselves become risk points. “I heard the other day about someone who got his network hacked from a refrigerator,” he said. “Whoever thought that you could get hacked from a refrigerator? But now, as refrigerators get smarter and people start connecting them to their networks, suddenly your fridge is a potential point of entry.”
- Employee browsing habits: If that’s not enough, companies also need to consider what’s referred to as “BYOD,” or Bring Your Own Device, when implementing cyber-security policies. “You have employees coming to work and using their PCs or smartphones to contact customers, suppliers and other employees,” Feakes said. Employees surfing social-media sites such as Facebook and YouTube on company computers create another potential opening for hackers. Employees’ own smartphones can also be used as hacking devices if they are logged into their company email accounts via a VPN. “You can see how this overlap can create potential risks,” Feakes concluded.
Basic Hackproofing Tips
All of the panelists agreed that one essential ransom-proofing protocol is the frequent use of backups—particularly off-site, cloud-based backups.
“I was having dinner with this fellow the other day,” Feakes recalled. “He said, ‘We’ve been ransomed twice this year.’ I asked him, ‘How did it go?’ He said, ‘We have well-tested, off-site backups, so both times we got ransomed, and they told us the ransom amount, we brushed it off. We rolled back to the previous day before the attack took place and went back to business as usual.’ So the company felt some pain, since missing a day of business is never fun, but it was spared the challenges that other companies have—basically by having off-site backups in place.”
Another way to help prevent malware attacks is to set clearly defined company policies governing the use of the internet on company devices.
“Most people think of the internet now as a right and not a privilege,” said Daryl Sirota, Estes Group vice president of managed services. “I would argue that we might need to reverse that thinking. The internet is a privilege. Only folks who have been properly trained and have appropriate equipment are allowed to surf the internet. You arguably might say that unless your job is researching parts and policies—or watching YouTube videos on how to install a carburetor, for instance—you probably shouldn’t have users on the internet, because they’ll eventually find the stupidest things out there and treat them as fact.

To keep data safe and secure in the case of a ransomware hack, regular backups to a remote (i.e., cloud-based) server as well as periodic firewall and penetration tests are recommended for businesses. Photo courtesy: Shutterstock.com
“When COVID hit, there were 14 million domains registered that looked like COVID information sites. Then the bad guys started spamming people with emails that said, ‘Hey, you need more information on COVID? Click here and we’ll take you to a site that looks like Johns Hopkins.’ If you didn’t properly patch your workstation, you got hacked, and it was a bad day. While social media isn’t necessarily bad, it can be a vehicle for malware, so defining your company’s internet-use policy is step number one.”
On a related note, Sirota advised against employees who work remotely using their own devices to access their employers’ networks, instead opting for company-issued devices that have the necessary firewalls and security extensions installed.
“If you are letting employees work from home, buying a Chromebook and letting them use a company device at home is more secure,” he said.
Another technique to minimize hacking could be referred to as “securing your perimeter.”
“Most of you have Wi-Fi,” Sirota said. “How far does that Wi-Fi signal travel? Maybe there’s a guy with a laptop sitting in a car in your parking lot. He might be hacking your Wi-Fi, which is a perimeter of your network. Don’t assume that just because it’s got WPA encryption, it’s safe. That encryption is only as good as the password. What if your password is your company name?”
Companies that use guest networks also need to take care to set up the necessary security systems to keep their proprietary data secure.
“We’ve seen cases where the guest network is just an extension of a corporate network,” Sirota said. “Sure enough, if you’re on the guest network, you can get in on corporate resources. You want to make sure that there’s a very strong firewall between your guest network and your real network.”
Finally, for companies that have the wherewithal, using more than one source for their cybersecurity needs is advisable.
“By definition, heterogeneous systems are more resilient,” Sirota noted. “You can’t rely on just a single technology to protect your business. You can’t just say ‘I’ve got a firewall, so I’m good,’ because many firewalls are set up improperly or are less secure. So maybe you use one vendor for the firewall and you have a different vendor for the antivirus tool. Maybe use a different vendor for doing penetration tests. Try to see everything from an outside perspective, because having an ‘outside’ set of eyes is going to be really valuable in this way.
“If you have only one set of eyes looking at the whole thing, you’re likely to catch what I call the fox watching the hen house.”
 About SEMA Education
About SEMA Education
Accessing SEMA’s industry-leading education is easier than ever. With dozens of live and on-demand offerings—and more debuting during the year—SEMA Virtual Education includes comprehensive presentations, insightful discussions, and short videos that teach, inform, inspire and entertain automotive specialty-equipment professionals. From builders and engineers to marketers and sales staff, participants will become more educated and prepared for success. To learn more, visit www.sema.org/virtual-education.